OpenTitan Root of Trust
OpenTitan® is a complete hardware root of trust design available under an Apache 2.0 licence. It is verified and validated to a commercial standard, and shipping in products from Google and others.
lowRISC® are the stewards of the OpenTitan project and have contributed to the project significantly.
![]()
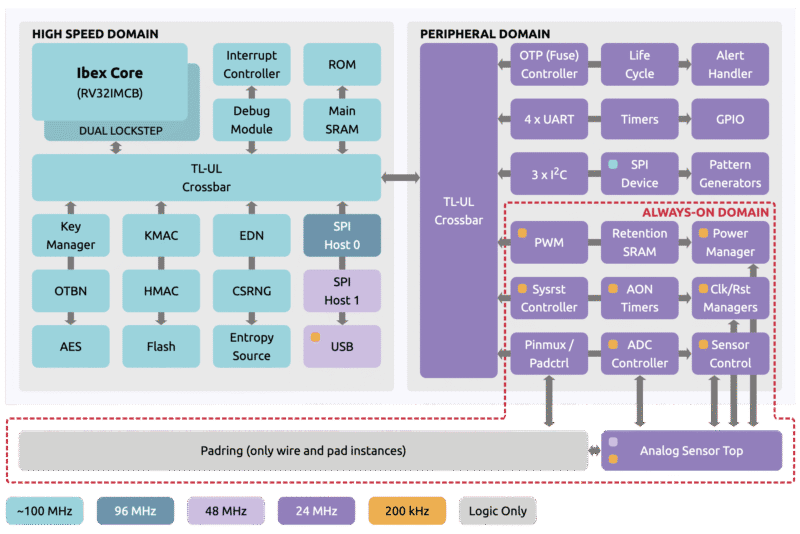
OpenTitan implements a complete microcontroller design with a CPU, memory, system and peripheral IP. It was created as a ”clean room” design from the ground up, and its security features are deeply embedded in its architecture and all of its components.
OpenTitan is hardened against side channel analysis (SCA) and fault injection (FI) attacks, and has been designed to meet the requirements of security certifications such as FIPS and Common Criteria, which shows the high quality of its design and documentation.
The OpenTitan project members believe in security by design. By making the OpenTitan RTL open-source, both product manufacturers and consumers can be confident in its quality. In addition, OpenTitan is used by academia, chip makers, tools vendors and friendly hackers, who use responsible reporting policies for any vulnerabilities they may find, helping us to continuously improve the design.
Discrete and integratable top-levels
OpenTitan is currently available as two top levels:
Some companies prefer to integrate OpenTitan IP components on their SoCs to add security capabilities, or simply because of their quality, transparency and accessibility.
Technical details
Ibex® CPU
In dual-core locked step configuration with Enhanced Physical Memory Protection (ePMP). Its security features include:
- Low-latency memory scrambling on the instruction cache and path to OTP, Flash, ROM and SRAM
- Data independent timing
- Dummy instruction insertion
- Bus and register file integrity
- Hardened program counter
Security IP
Including AES, HMAC, KMAC, CSRNG, key manager and a programmable big number accelerator for RSA and ECC (OTBN). In addition, OpenTitan features system-level security features such as a manufacturing life cycle manager and an alert handler for handling critical security events.
Software
- Boot ROM code implementing secure boot and chip configuration
- Bare metal top-level tests
- SCA and FI hardened Crypto Library with accelerated standard algorithms like AES, KMAC, HMAC, SHA, ECC, RSA, and more
- SPHINCS+ PQC-secure boot using a stateless hash-based signatures scheme
Designing SoCs based on OpenTitan
Designing a secure SoC based on OpenTitan requires significant security expertise, and access to analog IP (e.g. entropy source, sensor top), foundry IP (e.g. memories, power) and vendor-specific software. This IP is proprietary to silicon vendors and foundries, and typically commercial and/or closed-source.
Achieving certification against security standards requires considerable effort, and engagement with specialized security labs.
If you decide to design a chip based on OpenTitan we strongly recommend that you become an OpenTitan member. As a member you get access to expertise from lowRISC and existing members who have already taken the design to production. Members also get access to extra deliverables and documentation that significantly reduce their cost and effort in the design and certification of their product. If you are interested in joining as a member, contact us.
Availability of OpenTitan devices
OpenTitan Earl Grey discrete chips from Nuvoton are used in several Google products and services. In addition, Rivos announced the use of the Darjeeling integratable subsystem in their production server SoCs. These chips are not open-market parts.
The easiest way to start developing with OpenTitan is by simulating it in Verilator or synthesizing it on an FPGA on a supported evaluation board.
OpenTitan roadmap
lowRISC and other OpenTitan members continue to invest in the OpenTitan project. During 2026 and 2027 we are actively working on new features, including enhanced post-quantum cryptography (PQC) capabilities, new peripheral interfaces such as I3C, support for smaller process nodes and several other enhancements.
We are also running other open-source projects such as COSMIC to create new IP and improve the quality and efficiency of our products and processes. The outputs of these projects will benefit OpenTitan in the future. Our roadmaps are based on interest from existing and potential partners. If you would like to help steer the future direction of OpenTitan, contact us.
Contact